The imitation game
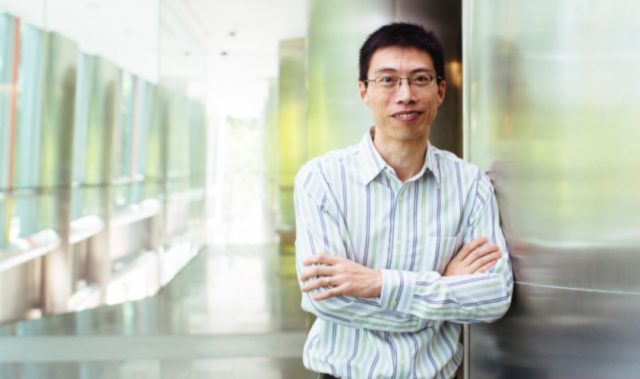
Inter-keystroke timing, or the time it takes between two consecutive key presses, is the most commonly used type of data for keystroke biometrics. Professor Gao and colleagues set out to question the “uniqueness property” of keystroke biometrics—the extent to which systems can be fooled by attackers imitating their victims’ typing patterns.
Recruiting 84 SMU students as attackers, the researchers first gave each participant 30-45 minutes of training with a feedback software program, Mimesis, which they had developed. The program gives positive or negative feedback to the student so that, through incremental adjustments, they can closely imitate how their victim types.
Consider a scenario where a biometrics database is compromised; software such as Mimesis could be used to extract victims’ typing parameters, which can then be used for malicious purposes.
“For example, it will tell you that the way that you type right now is slightly different from the victim’s typing; or the inter-keystroke timing between A and S is shorter than what the victim types, so you better slow down a little bit when you are typing these two letters,” Professor Gao elaborates.
The results show that when a victim’s typing pattern is known, imitation is possible—contrary to the findings of previous studies. The students could easily log into systems by impersonating their would-be victims, and 14 of them managed to do so with an almost 100% success rate over a total of 200 attempts.
Interestingly, even if the attacker had partial information about their victim—perhaps a handful of typing samples captured by a key-logger as the victim is authenticating—they could nevertheless still achieve a reasonably high false acceptance rate.
Professor Gao presented this research at the 20th Annual Network & Distributed System Security Symposium 2013 in San Diego, California. His conference proceedings paper, ‘I Can Be You: Questioning the Use of Keystroke Dynamics as Biometrics’, bagged the Best Paper Award.
Designing better, more usable interfaces
From their experiments, the researchers also learned a number of fascinating things: for one, the easier the password, the easier the imitation. Male students were also found to be better than female students at imitation. However, various factors such as typing consistency, type of keyboard, and imitation strategy had much less influence on the imitation outcome than expected.
Findings such as these could potentially prompt a re-think of current keystroke biometrics-based authentication systems, Professor Gao believes. With his work, he hopes to spread awareness about the weaknesses of keystroke biometrics, allowing companies to configure their web services in such a way that provides functionality without compromising on end user privacy.
Asian Scientist Magazine is a media partner of the Singapore Management University Office of Research.
———
Copyright: SMU Office of Research. Read the original article here; Photo: Cyril Ng.
Disclaimer: This article does not necessarily reflect the views of AsianScientist or its staff.